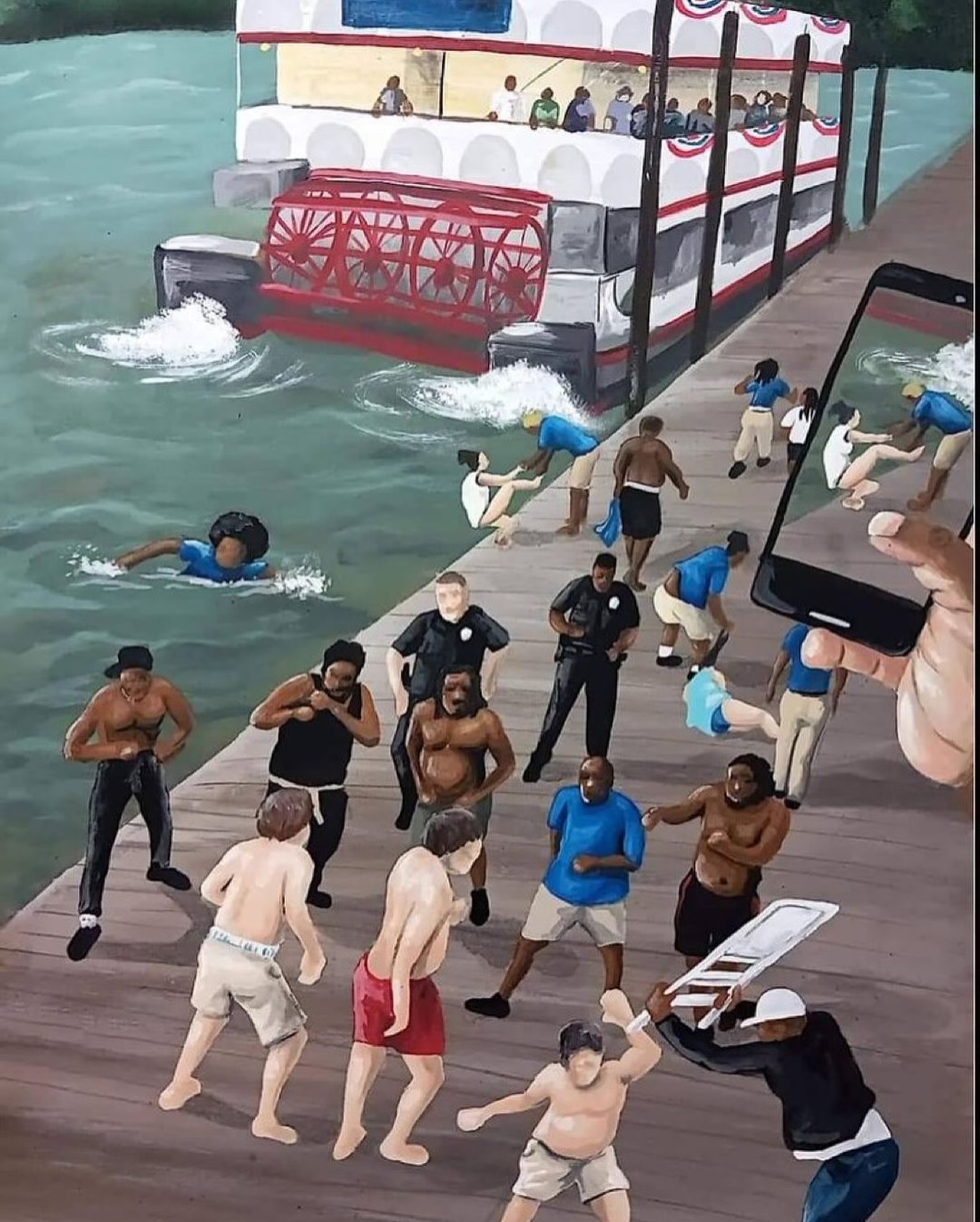
She won’t near the waters again :sob::joy:
Share
Comment
1 person reacted to this. Views 0
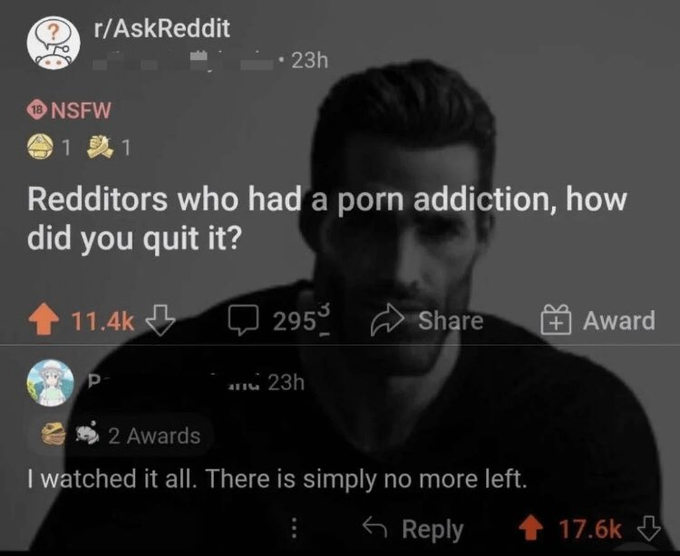
That is no excuse why your wife should be driving... :joy::joy::joy::joy:.
Is the police right or wrong?
Share
Comment
Views 2
:butterfly:°𙄠ð˜¿ð™¤ð™£'𙩠ð™ƒð™–ð™«ð™š 𘼠ð˜½ð™–ð™™ ð™ð™šð™¢ð™¥ð™šð™§ 𙄠ð™…ð™ªð™¨ð™© ð™ƒð™–ð™«ð™š 𘼠ð™Œð™ªð™žð™˜ð™ ð™ð™šð™–ð™˜ð™©ð™žð™¤ð™£ ð™ð™¤ ð˜½ð™ªð™¡ð™¡ð™¨ð™ð�... see more
:butterfly:°𙄠ð˜¿ð™¤ð™£'𙩠ð™ƒð™–ð™«ð™š 𘼠ð˜½ð™–ð™™ ð™ð™šð™¢ð™¥ð™šð™§ 𙄠ð™…ð™ªð™¨ð™© ð™ƒð™–ð™«ð™š 𘼠ð™Œð™ªð™žð™˜ð™ ð™ð™šð™–ð™˜ð™©ð™žð™¤ð™£ ð™ð™¤ ð˜½ð™ªð™¡ð™¡ð™¨ð™ð™žð™©âœÂ°Û°
°Butterfly ( t.me
Share
Comment
Views 0

 Please Wait..
Please Wait..